The Definitive Guide to OT Security Assessments: 5 Critical Blind Spots and the PulseCheck Solution
Executive Summary: Navigating the 2026 Industrial Threat Landscape
In the high-stakes environment of Critical Infrastructure, “visibility” is often a hollow buzzword. For most industrial operators, the network is still a “Black Box” a collection of legacy hardware, undocumented bridges, and silent threats. This guide explores why a surgical OT security assessment is the only defense against modern cyber-physical threats and how the PulseCheck method provides the clarity needed for 2026’s regulatory and threat landscape.
Introduction: The State of Industrial Cyber Risk
In the world of Operational Technology (OT), there is a phrase that keeps directors and C-suite executives up at night: “The Black Box.” It refers to those segments of your network, perhaps a legacy manufacturing floor, a remote utility station, or a complex web of third-party vendor connections—where visibility goes to die.
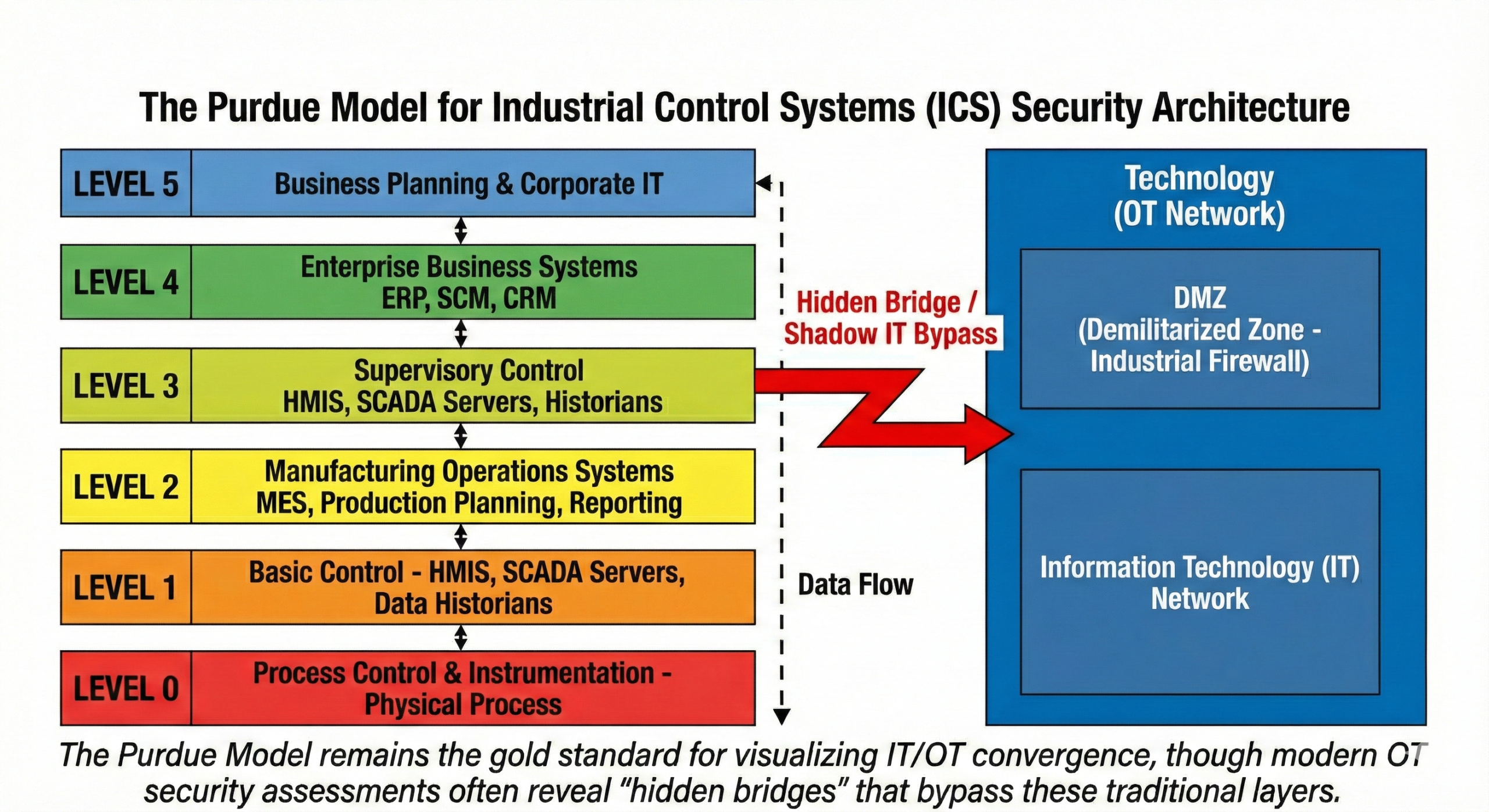
To drop this uncertainty, a proactive OT security assessment is no longer just the best practice; it is a fundamental requirement for operational survival. As we move through 2026, the convergence of IT and OT has dissolved the traditional perimeter. The “airgap” is a relic of the past, replaced by a hyper-connected ecosystem where a single compromised sensor can halt a global supply chain.
Many organizations work under the dangerous assumption that their systems are secure because they are “air-gapped” or because no automated alerts have been triggered. However, silence is rarely a sign of safety. In the realm of industrial control systems (ICS) security, silence usually means a threat actor is currently in their “dwell time” in the period where they sit quietly, mapping your vulnerabilities and preparing for a strike. To achieve true cybersecurity resilience, you must address the five critical blind spots that our PulseCheck method is designed to expose.
1. The “Dwell Time” Trap: Hidden in Plain Sight
The most sophisticated cyberattacks don’t happen in minutes; they happen over months. The goal of a modern adversary is not immediate disruption, but persistent, undetectable access.
Living off the Land (LotL)
Threat actors today use “Living off the Land” techniques. Instead of deploying loud, easily detectable malware that triggers signature-based defenses, they use your own administrative tools like PowerShell, WMI, or remote desktop protocols (RDP)to move laterally.
Because these actions look like “normal” administrative behavior, standard passive monitoring tools often ignore them. They don’t trigger alarms because, on paper, it looks like your own team is performing maintenance. Recent data from the Dragos 2026 OT/ICS Cybersecurity Report highlights that adversaries are staying internal for longer periods, often exceeding 200 days before detection.
How PulseCheck Solves It
A standard OT security assessment might just look for known vulnerabilities. PulseCheck replaces passive waiting with active threat hunting services.
- Behavioral Analysis: We look for “impossible travel” patterns and credential misuse across the control plane.
- Log Correlation: We ingest data from disparate sources to find the narrative of an attack that standard SIEMs miss.
- Egress Testing: We find if your PLCs are trying to “phone home” to suspicious external IPs, a classic sign of beaconing.
2. The Myth of the Airgap and IT/OT Convergence
In the age of digital transformation and Industry 4.0, the airgap is largely a myth. Your HVAC systems, PLC controllers, and smart sensors are increasingly connected to your enterprise IT network for data harvesting, remote monitoring, and maintenance.
The Pivot Point
This IT/OT convergence creates a massive, unmanaged attack surface. An attacker who breaches a low-security workstation in your marketing or HR department can often pivot through internal switches into your water treatment controls or production line.
According to CISA’s latest advisories, the lack of segmentation between business and process networks remains a primary vulnerability. If you don’t have a 100% accurate hard asset inventory, you are defending a map that doesn’t exist.
Hard Asset Inventory vs. Logical Discovery
A comprehensive OT security assessment must provide more than just a list of IP addresses. PulseCheck provides a surgical mapping of:
- Physical Assets: Every chassis, backplane, and module version.
- Logical Connections: Visualizing which IT assets have the “rights” to talk to which OT assets.
- Hidden Bridges: Finding unauthorized dual-home machines (e.g., a PC with both Wi-Fi and a hardline to the PLC) that bypass your expensive firewalls.
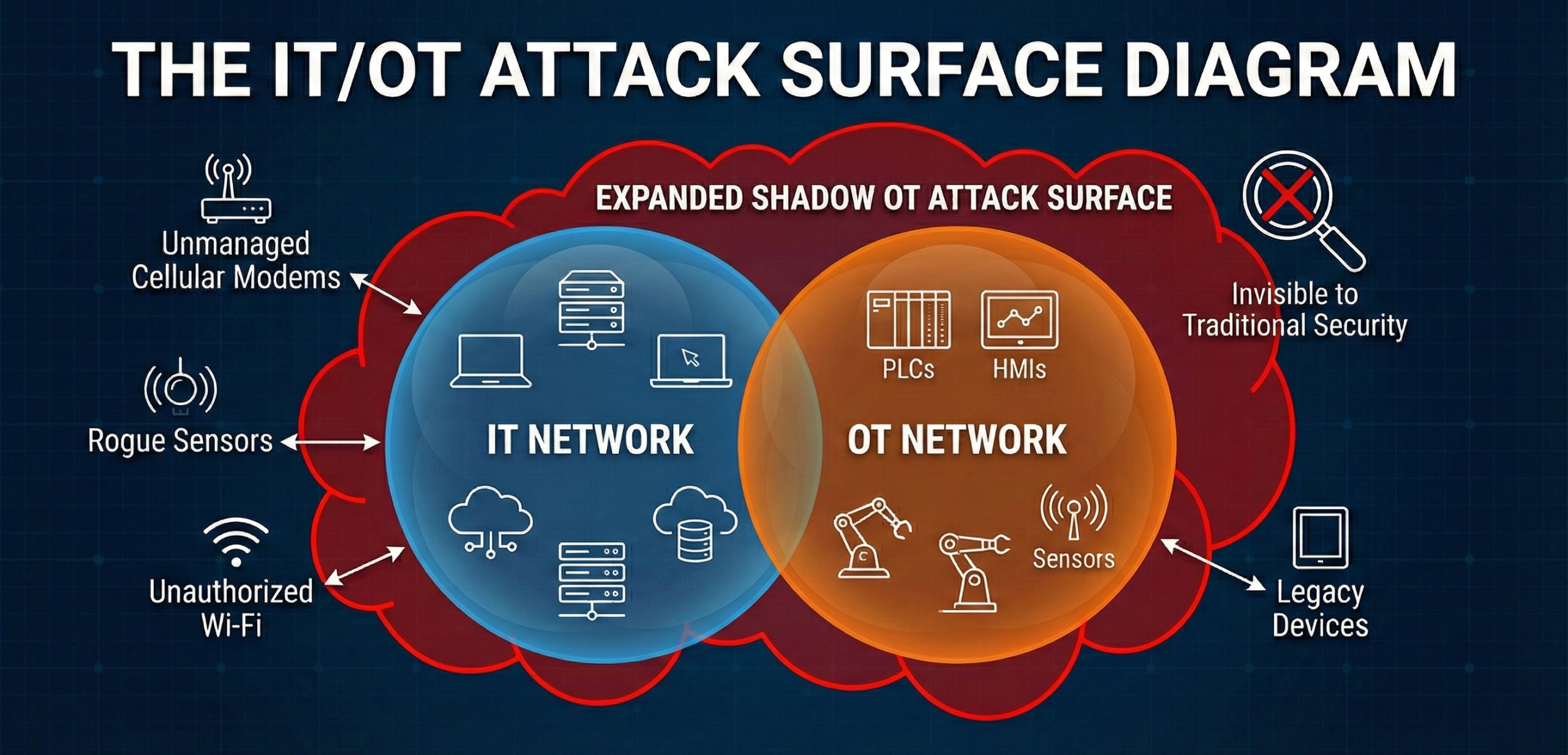
3. Shadow Industrial Devices and Rogue Access
“Shadow IT” has long been a headache for CIOs, but “Shadow OT” is a catastrophe for plant managers. These are devices that live on your wires but don’t appear in your documentation.
The Rise of Unmanaged Entry Points
Operational environments are dynamic. Maintenance teams often prioritize uptime over security protocol. This leads to:
- Temporary Maintenance Laptops: Plugged into a controller “just for a minute” to run diagnostics but left connected or infected.
- Cellular Modems: Installed by third-party vendors for “easy remote support” without the knowledge of the security team.
- Legacy Sensors: Devices that were supposed to be decommissioned years ago but are still broadcasting data.
These unauthorized access points are open doors. They often bypass your primary firewalls and security protocols, creating an unmonitored “backdoor” into your most sensitive operations.
Surgical Discovery
Our OT security assessment doesn’t just scan; it interrogates. We use non-disruptive, industrial-grade discovery methods to find rogue hardware and unauthorized remote access tools. We find the cellular “pucks” hidden in the back of cabinets that are quietly broadcasting your internal traffic to the public internet.
4. Prioritization Paralysis: The “PDF Problem”
One of the biggest failures of the cybersecurity industry is the “Compliance Dump.” Many security firms offer a standard OT security assessment that results in a 500-page PDF finding thousands of “critical” issues.
Why More Data is Sometimes Worse
For a busy operations team, this leads to paralysis. If everything is a priority, nothing is. Most OT teams are understaffed; they cannot patch 1,000 vulnerabilities during a single maintenance window.
The PulseCheck Prioritization Roadmap
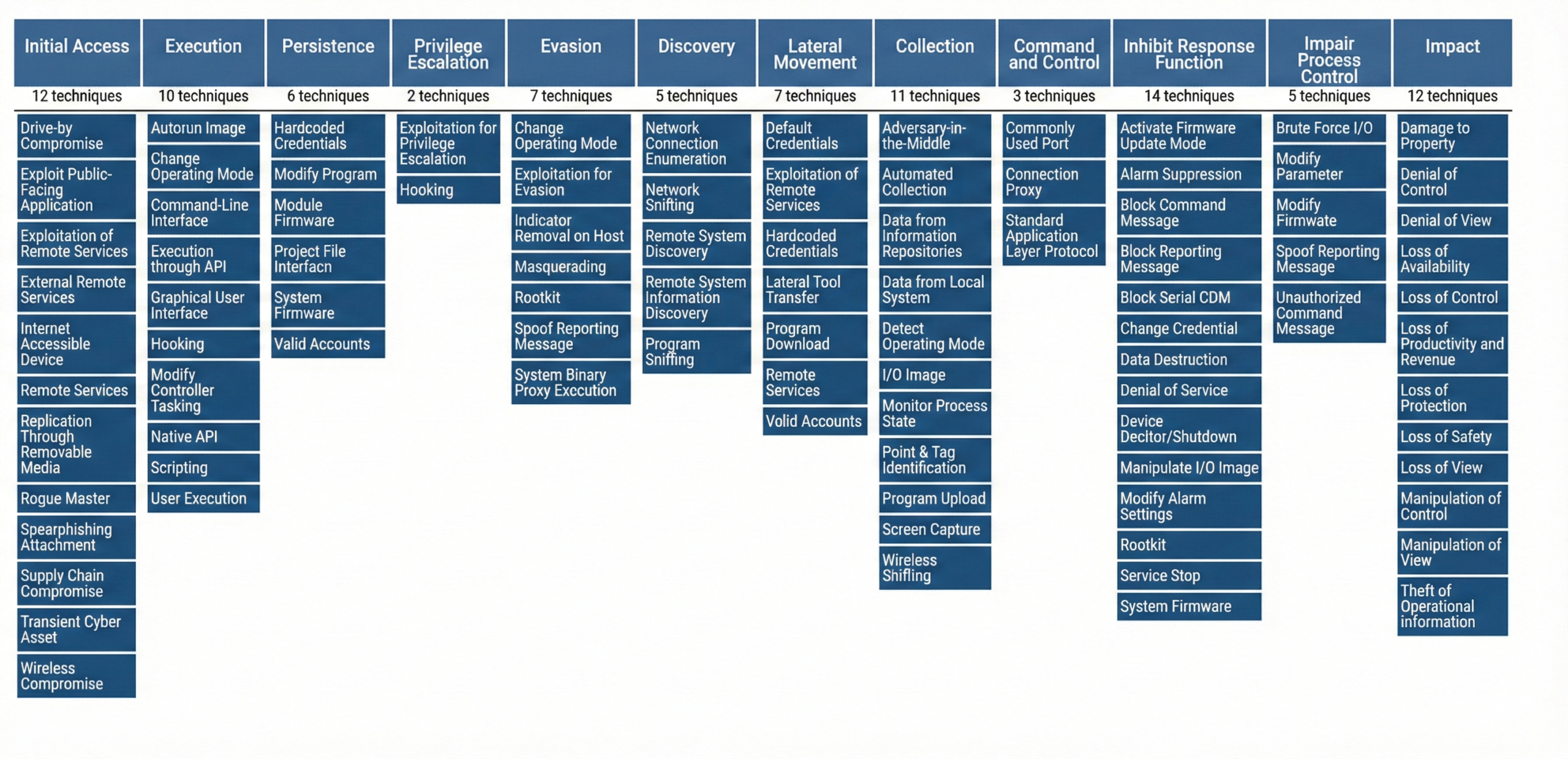
We don’t just find gaps; we analyze them through the lens of operational reality. We utilize the NIST Cybersecurity Framework (CSF) and the MITRE ATT&CK for ICS framework to categorize risks based on their potential to cause physical disruption.
Risk Category | Impact on Production | Remediation Urgency |
Safety Critical | Potential for Physical Harm/Explosion | Immediate (24-48h) |
Production Critical | Potential for Line Stoppage/Loss | High (Next Maintenance Window) |
Information Risk | Data Leakage / Reconnaissance | Medium (Standard Cycle) |
PulseCheck tells you which specific vulnerabilities an attacker would actually use to shut down your production line. This allows you to focus your limited budget on the 20% of fixes that provide 80% of your protection.
5. The Compliance and Insurance “Proof Gap”
Regulatory bodies and cyber insurance providers (such as those enforcing NERC CIP, HIPAA, or CMMC) have changed their requirements. They no longer accept “best effort” security.
The Defensibility Gap
If a breach occurs and you cannot prove that you conducted a regular, surgical OT security assessment, the consequences are severe. Insurance carriers are increasingly denying claims if “due diligence” cannot be proven through documented audits.
Bridging the Gap with PulseCheck
PulseCheck provides the hard data, federal-grade validation, and executive-level reporting needed to satisfy auditors. We move your organization from a posture of “hoping for the best” to one of operational governance. We provide the “Artifacts of Compliance”—the documented proof that you are actively managing your risk.
Deep Dive: The PulseCheck Lifecycle
We understand that in critical infrastructure, uptime is not optional. A standard IT-style vulnerability scan can crash legacy PLCs. PulseCheck was built from the ground up to be “OT-Safe.”
Step 1: Process-Aware Scoping
We begin by understanding your process. We don’t just look at IPs; we look at your P&IDs (Piping and Instrumentation Diagrams) to understand the physical impact of a digital failure.
Step 2: Passive & Low-Energy Discovery
Using federal-grade passive and low-energy active discovery, we build a 1:1 digital twin of your network architecture. This allows us to find the “blind spots” without ever knocking a device offline.
Step 3: Vulnerability Synthesis
We cross-reference your assets against the latest SANS Institute ICS security research and the National Vulnerability Database (NVD). We find the CVEs that actually matter to your specific firmware versions.
Step 4: Active Threat Hunting
While others look for vulnerabilities, we look for activity. We hunt for the artifacts of compromise, stolen credentials, lateral movement, and command-and-control (C2) traffic.
Step 5: The Strategic Roadmap
We deliver a roadmap that is readable by both the C-suite and the plant floor. No 500-page PDFs. Just clear, actionable steps to secure your future.
The UnRavl Difference: Federal-Grade Integrity
UnRavl isn’t a commodity MSP. We are strategic integrators bringing DoD-level technology invented by former NSA and DHS leaders, directly into the private sector.
When you run a PulseCheck, you aren’t just buying a service; you are buying clarity. A formal OT security assessment is the foundation of a modern security posture. You are gaining the ability to tell your stakeholders, your customers, and your board: “We know where we are weak, and we have a definitive plan to fix it.”
Frequently Asked Questions (FAQ)
What is the difference between an IT audit and an OT security assessment?
An IT audit focuses on data confidentiality and integrity (CIA triad). An OT security assessment prioritizes Availability and Safety. In OT, we cannot simply “reboot” a system if a scan goes wrong. Our tools are specifically designed to communicate with sensitive industrial protocols without causing latency or crashes.
How often should we conduct a PulseCheck?
The threat landscape in 2026 moves fast. We recommend a full OT security assessment annually, with quarterly “delta” checks to account for network changes, new vendor connections, or firmware updates.
Will PulseCheck cause downtime?
No. Our method is built on “Zero-Impact” discovery. We prioritize passive monitoring and only use active interrogation on devices we have verified that can handle the traffic.
Conclusion: Stop Guessing, Start Knowing
“I don’t know” is a liability your business can no longer afford. Every day that passes without a comprehensive OT security assessment is another day a threat actor could be sitting in your network, unnoticed.
PulseCheck turns your network from a black box into a transparent, defensible asset. In an era of escalating digital risk, clarity is your greatest competitive advantage.
Contact UnRavl today to schedule your PulseCheck OT Threat Hunt.
Discover Your True Risk Profile
Stop guessing. Start knowing. Whether you need to secure industrial operations, protect enterprise data, or navigate complex compliance requirements, we bring clarity to complexity.