5 Strategic Advantages of IT/OT Convergence for Global OT Security
In the modern industrial landscape, the air gap is no longer a physical reality; it is a digital myth. As we move deeper into 2026, OT Security has transitioned from a niche concern of plant managers to a boardroom priority. The integration of smart sensors, cloud analytics, and remote monitoring has made OT Security the linchpin of global infrastructure. Without robust OT Security protocols, the very systems that provide our water, electricity, and manufacturing capabilities remain vulnerable to increasingly sophisticated actors.
The evolution of OT Security requires a fundamental shift in how we view the factory floor. We are no longer just protecting isolated machines; we are securing a global data fabric. To maintain OT Security, organizations must adopt a “Security by Design” philosophy that treats every sensor and actuator as a potential entry point. The stakes of OT Security have never been higher, as a single breach can lead to physical environmental disasters or loss of life. Consequently, OT Security is now the primary metric for operational excellence in the 21st century.
The Evolution of the Industrial Landscape
Historically, Operational Technology (OT) relied on “security through obscurity.” Proprietary protocols and isolated networks meant that OT Security was often overlooked in favor of uptime. However, the dawn of Industry 4.0 has forced an IT/OT Convergence that brings standard networking protocols into the plant floor. While this transition drives efficiency, it also expands the attack surface.
Today, ICS Security (Industrial Control Systems Security) is no longer just about protecting a PLC (Programmable Logic Controller); it is about securing the entire data pipeline. To achieve true Cybersecurity Resilience, organizations must move away from reactive “patch-and-pray” mentalities and toward proactive Threat Hunting and continuous monitoring.
I. Understanding IT/OT Convergence: The Double-Edged Sword
The merging of IT and OT environments is the most significant shift in industrial history since the introduction of the PLC. IT/OT Convergence allows for real-time data visibility, predictive maintenance, and streamlined supply chains. However, it also means that a ransomware infection in the corporate billing department can now technically—and physically—halt a production line.
The Cultural Gap
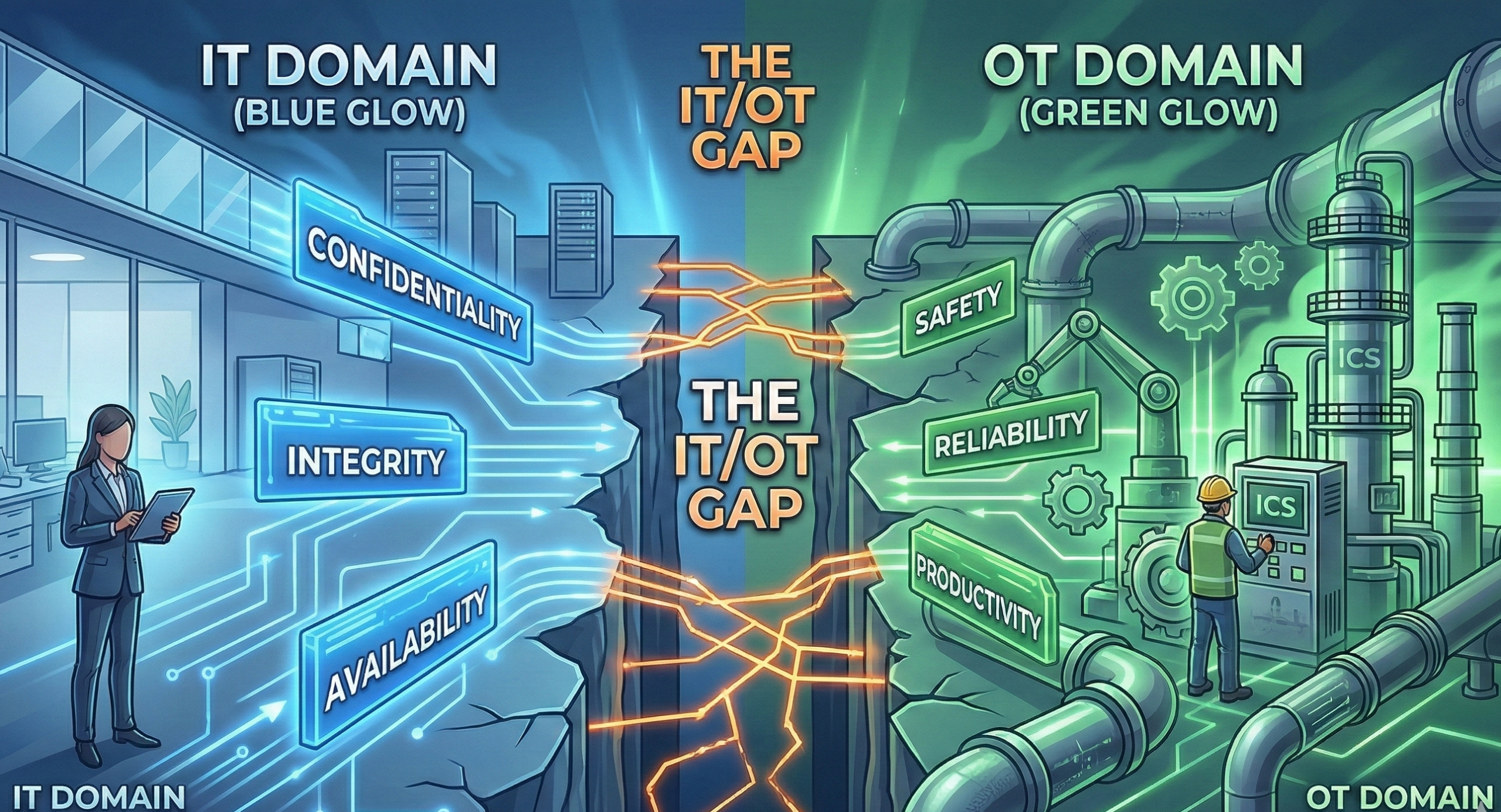
One of the biggest hurdles in IT/OT Convergence isn’t the technology; it’s the people.
- IT Teams prioritize Confidentiality, Integrity, and Availability (The CIA Triad).
- OT Teams prioritize Safety, Reliability, and Productivity (The SRP Triad).
Bridging this gap is essential for Cybersecurity Resilience. When IT tries to push a standard patch cycle on a turbine that hasn’t been shut down in three years, the friction is palpable. Success requires a unified governance model where OT Security is treated as a specialized discipline, not just “IT for old computers.”
II. The Pillars of ICS Security
ICS Security focuses on the hardware and software that coordinates the physical world. This includes SCADA systems, Distributed Control Systems (DCS), and PLCs. Unlike standard IT assets, these devices often have lifespans of 20 to 30 years.
Legacy Systems and Vulnerabilities
Many components under the ICS Security umbrella were designed before the internet was a household utility. They lack encryption, use default passwords, and often communicate in “clear text” protocols like Modbus or DNP3. To understand the baseline requirements for these environments, practitioners often look to the NIST Guide to Industrial Control Systems (ICS) Security, which outlines the unique risk management processes required for physical processes.
To protect these, we utilize:
- Network Segmentation: Using the Purdue Model to isolate levels of the factory floor.
- Unidirectional Gateways: Ensuring data can flow out for analysis, but threats cannot flow in.
- Virtual Patching: Using IPS (Intrusion Prevention Systems) to shield unpatchable legacy devices.
III. From Defense to Offense: Threat Hunting in the Plant
If you are only waiting for an alarm to go off, you’ve already lost. Proactive Threat Hunting is the process of searching through networks to detect and isolate advanced threats that evade existing security solutions.

How to Hunt in an OT Environment
In an OT context, Threat Hunting looks different than in IT. You aren’t just looking for unusual file executions; you are looking for:
- Atypical Logic Changes: Did a PLC code change occur outside of a maintenance window?
- Protocol Anomalies: Is a device communicating via a protocol it doesn’t usually use?
- Baseline Deviations: Is a sensor “chattering” more than usual, signaling a potential Man-in-the-Middle attack?
By integrating Threat Hunting into your daily operations, you shift the burden of proof onto the attacker, making it harder for them to maintain persistence within your network. For a structured approach to identifying these behaviors, security teams leverage the MITRE ATT&CK® for ICS, which maps specific adversary techniques to industrial impacts.
IV. Engineering Cybersecurity Resilience
Cybersecurity Resilience is the ability to anticipate, withstand, recover from, and adapt to adverse conditions, stresses, or attacks on systems. In the world of OT Security, resilience is measured by how quickly you can return to a “Safe State” after a compromise.
Building the Resilient Framework
- Incident Response for OT: You cannot simply “wipe and reload” a blast furnace. Your IR plan must be OT-specific, focusing on manual overrides and mechanical fail-safes.
- Redundancy: Physical redundancy of critical controllers ensures that a digital failure doesn’t lead to a physical catastrophe.
- Continuous Monitoring: Passive monitoring tools allow you to see what is happening on the wire without the risk of “pinging” a sensitive legacy device into a crash.
V. Advanced Threat Hunting: The “Crown Jewel” Methodology
In an industrial environment, Threat Hunting is not about chasing every alert; it is about protecting the “Crown Jewels” the processes that, if disrupted, lead to catastrophic failure.
Step 1: Establishing the Telemetry Baseline
You cannot hunt what you cannot see. Effective Threat Hunting in ICS Security requires a deep understanding of what “normal” looks like.
- Packet Inspection: Capturing traffic at the Level 2 and Level 3 switches of the Purdue Model.
- Asset Inventory: Knowing every MAC address, IP, and firmware version on the plant floor.
- Process Variables: Monitoring the actual physical limits (temperature, pressure, RPM) to detect “Living off the Land” attacks.
Step 2: Hypothesizing the Attack Vector
A hunter assumes the perimeter has already been breached via IT/OT Convergence points. A common hypothesis might be: “An attacker has gained access to the Engineering Workstation (EWS) via a compromised VPN and is attempting to push a malicious logic update to the PLC.”
VI. Hardening the Architecture: From Air Gaps to Zero Trust
The concept of IT/OT Convergence has effectively killed the traditional air gap. In its place, we must implement a Zero Trust Architecture (ZTA) tailored for industrial needs.
Identity and Access Management (IAM)
In many legacy plants, shared passwords for HMIs (Human Machine Interfaces) are common. To achieve Cybersecurity Resilience, these must be replaced with:
- Role-Based Access Control (RBAC): Restricting access based on job function.
- Multi-Factor Authentication (MFA): Essential for any remote access gateway.
Micro-Segmentation
Standard ICS Security often segments by VLANs, but Cybersecurity Resilience requires going deeper. Micro-segmentation allows us to isolate a single compromised PLC without shutting down the entire assembly line. This “Cell/Area” isolation is the cornerstone of modern OT Security. To implement these controls effectively, many global organizations align with the ISA/IEC 62443 Series of Standards, which provides a multi-layered approach to security levels.
VII. The Role of Artificial Intelligence and Machine Learning
As IT/OT Convergence accelerates, the sheer volume of data becomes too much for human analysts. AI is now being integrated into OT Security platforms to automate Threat Hunting.
Behavioral Analytics
Instead of looking for known “signatures” (which are rare in bespoke industrial attacks), AI looks for behavioral shifts. If a valve that usually opens 10% suddenly opens 90% during a period of low demand, the AI flags this as a potential ICS Security incident. This automated detection is vital for maintaining Cybersecurity Resilience in complex, high-speed manufacturing environments.
VIII. Incident Response: The “Break Glass” Scenario
The ultimate test of Cybersecurity Resilience is the Incident Response (IR) plan. Unlike IT IR, OT IR must include “Safety-Instrumented Systems” (SIS).
The Recovery Hierarchy
- Safety First: Ensure the physical process is in a non-volatile state.
- Manual Control: Shift to manual overrides if the digital layer is compromised.
- Isolation: Sever the IT/OT Convergence links to prevent lateral movement.
- Forensic Preservation: Capture volatile memory from PLCs before a reboot.
IX. Conclusion: The Path Forward for Industrial Leaders
Achieving excellence in OT Security is a marathon, not a sprint. The integration of ICS Security into the broader corporate risk profile is no longer optional. By embracing IT/OT Convergence with a critical eye, investing in proactive Threat Hunting, and building a culture of Cybersecurity Resilience, organizations can protect not just their data, but their physical legacy.
The future of industry is connected, but it must also be protected. The bridge between the digital and physical worlds is built on the strength of your OT Security strategy.
Discover Your True Risk Profile
Stop guessing. Start knowing. Whether you need to secure industrial operations, protect enterprise data, or navigate complex compliance requirements, we bring clarity to complexity.
